from IP theft with Stunnix C/C++ Obfuscator
Download
C/C++ Obfuscator
evaluation notes | what is new in current version | Previous versions
Interactive obfuscation of files of various types
Use controls at the right to see how different options affect result of obfuscation; use player-like buttons to navigate between samples and to control playback.
PROTECTION
Identifiers:
Strings:
Comments:
|
||
Pricing
Evaluation
edition
edition
FREE
- Evaluation use only
- Expires in 3 monthes
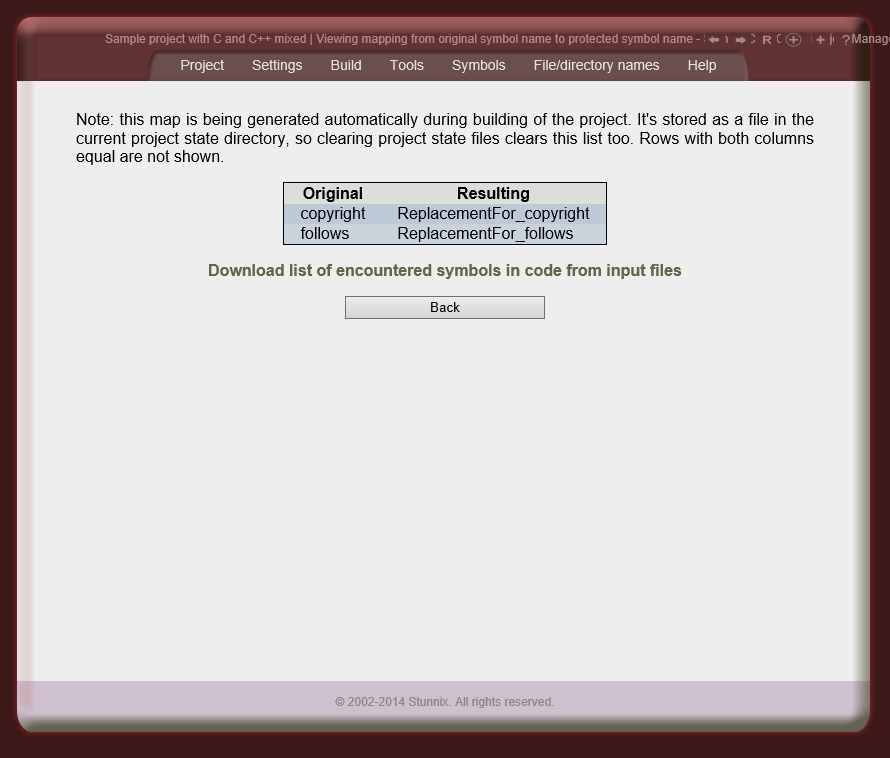
- Instead of mangling, ReplacementFor_ gets prepended to symbols
Single developer
edition
edition
$539
- Can be used by only 1 developer
- Does not expire
-
All features are available.
Enterprise
edition
edition
Contact us
- All developers can use it
- Does not expire
-
All features are available.
More on pricing and licensing terms.
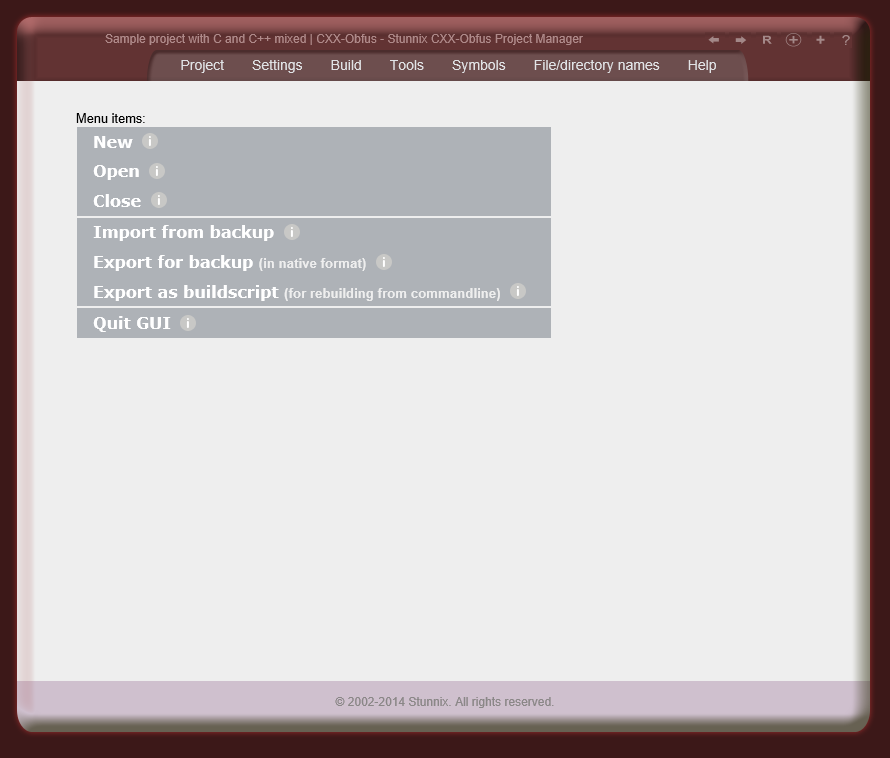
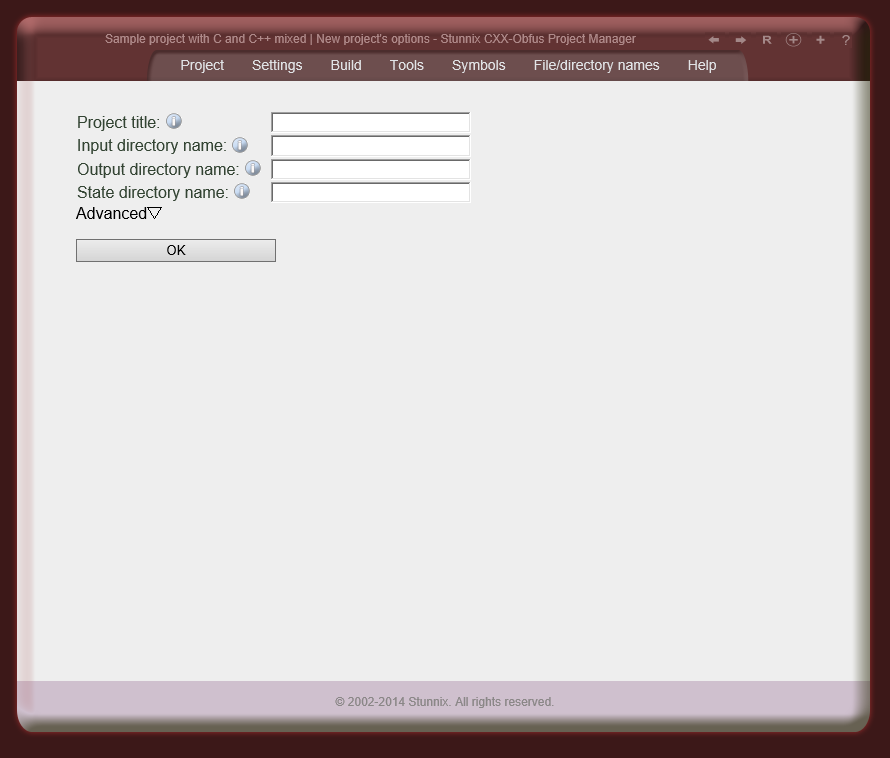
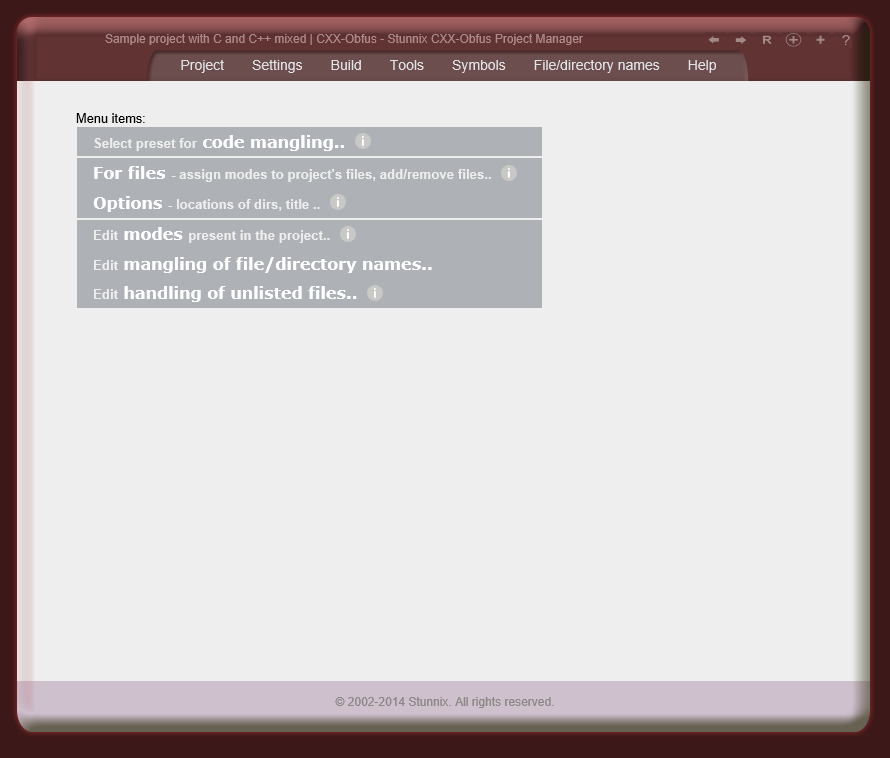
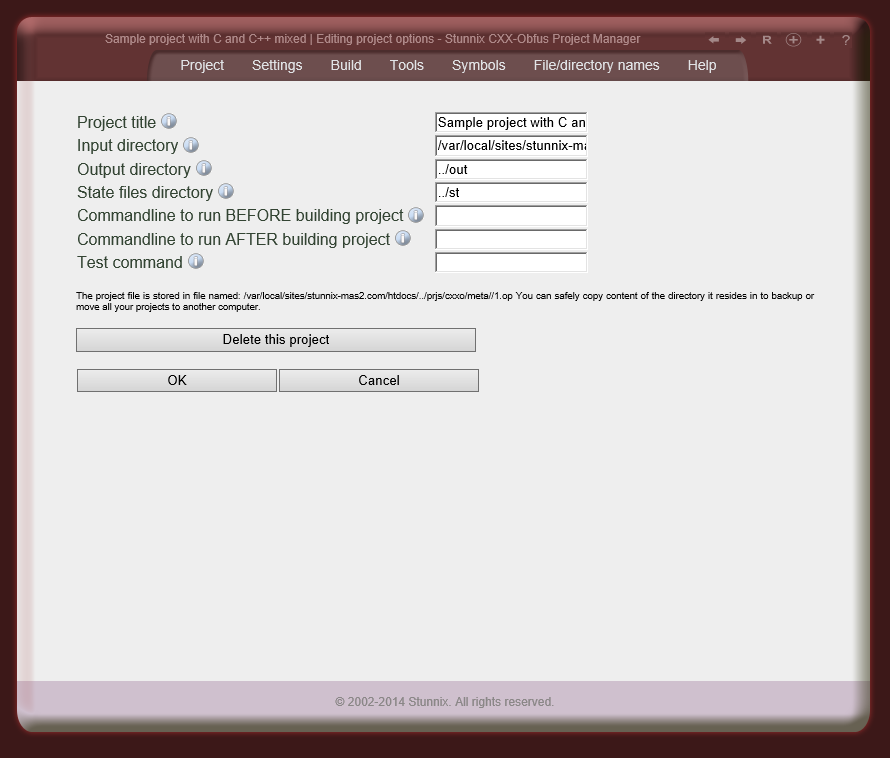
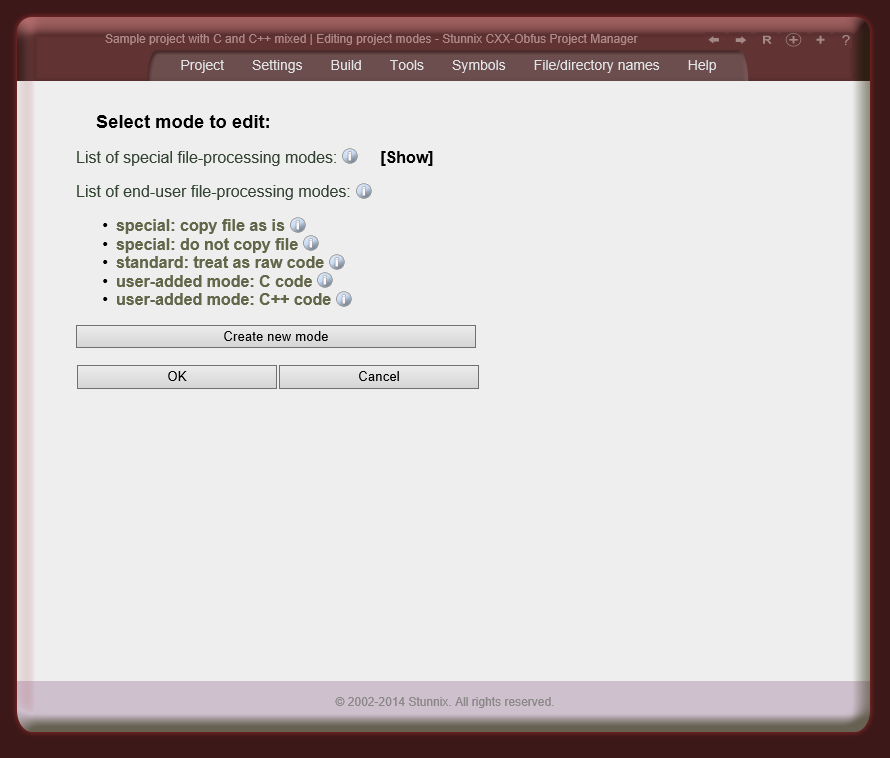
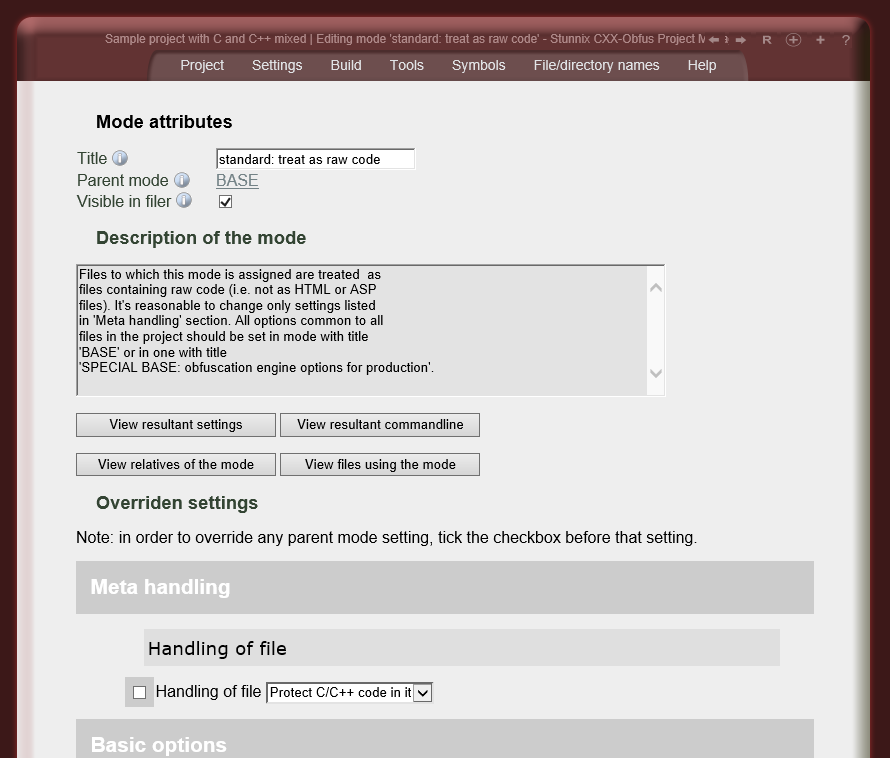
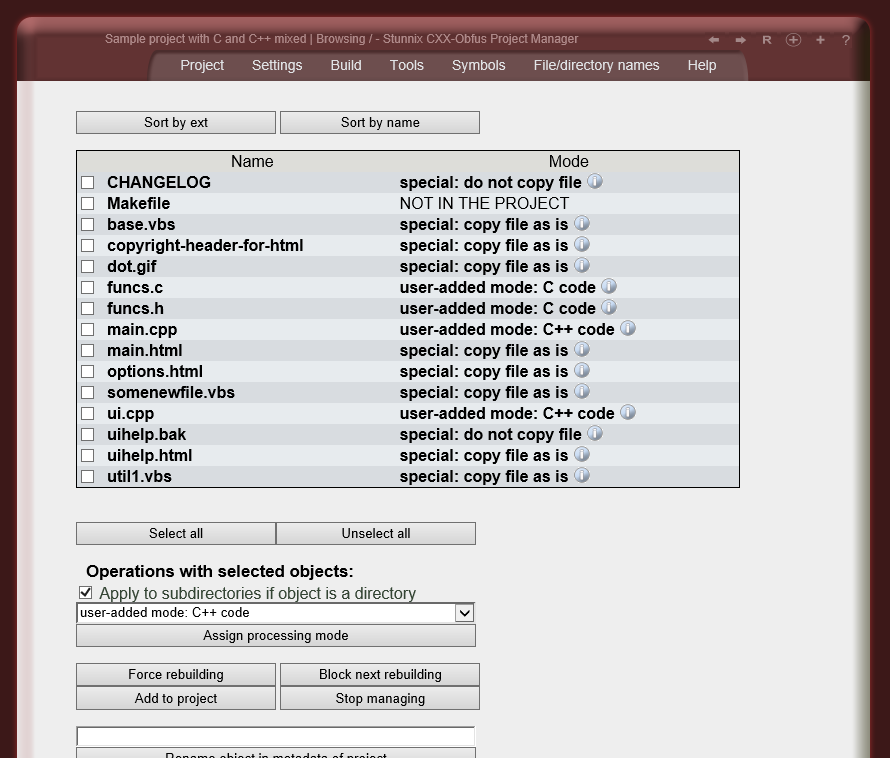
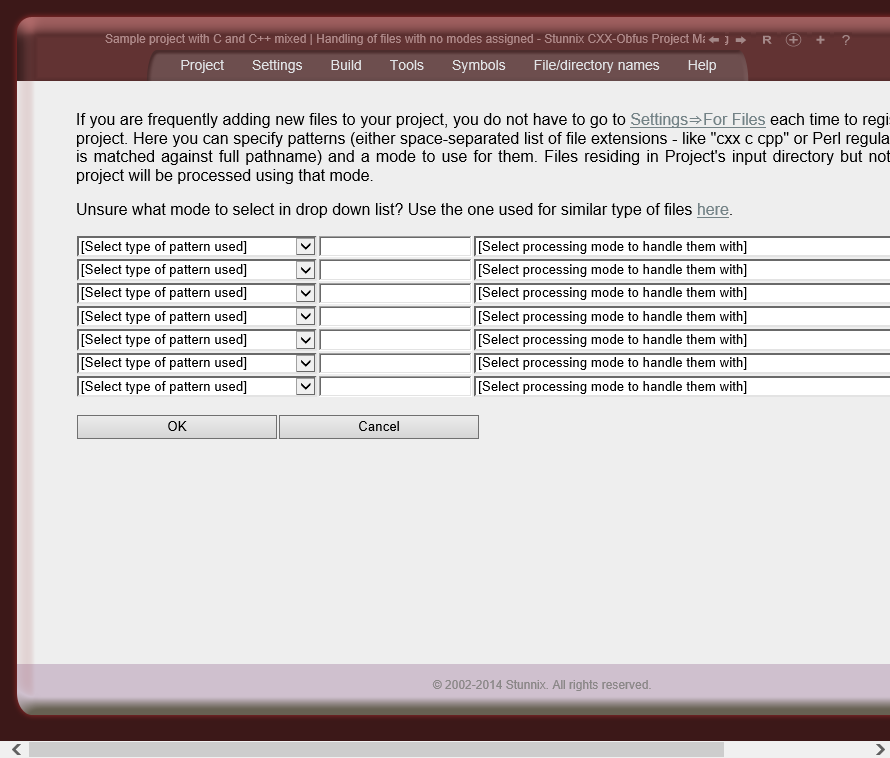
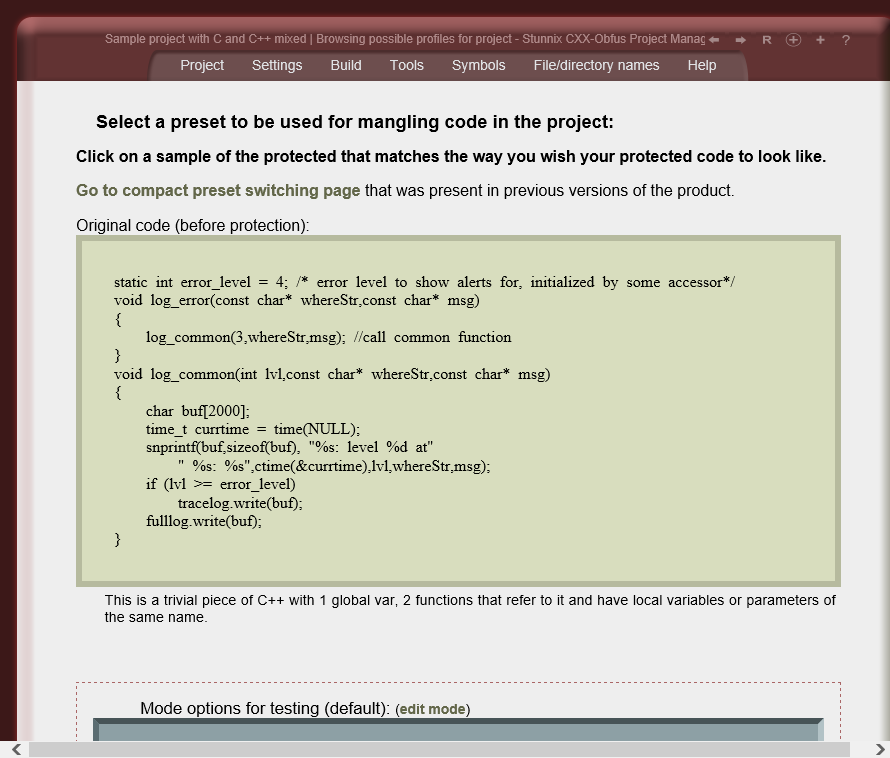
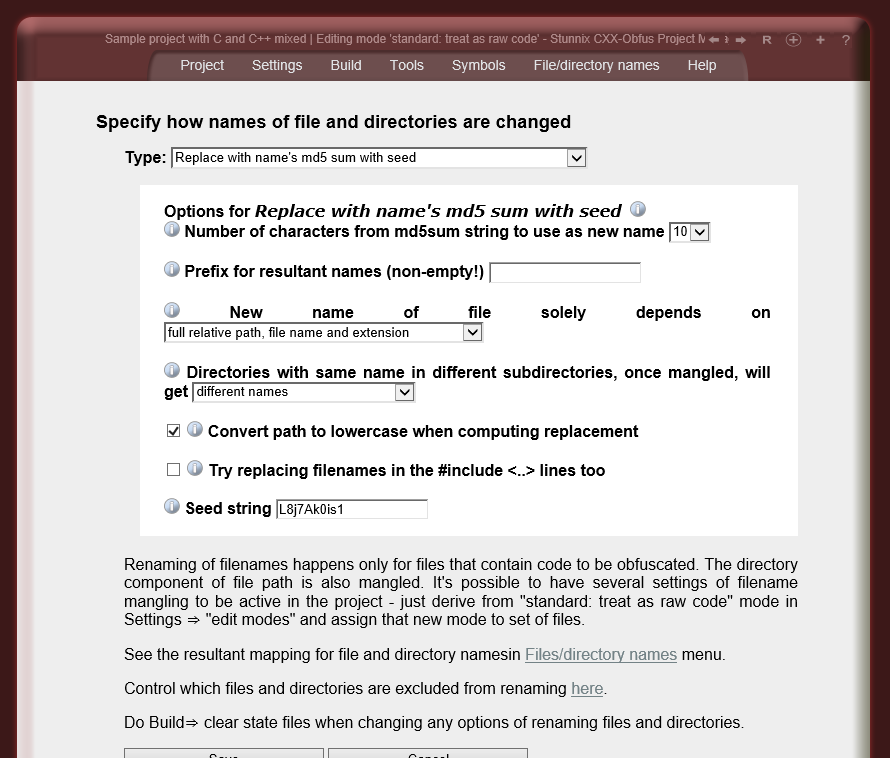
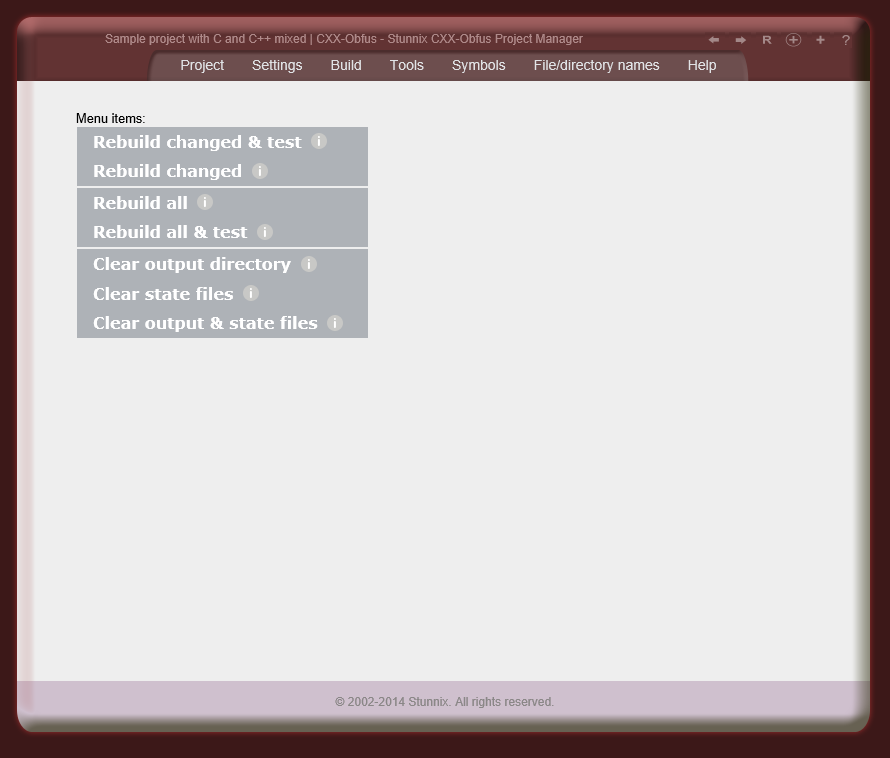
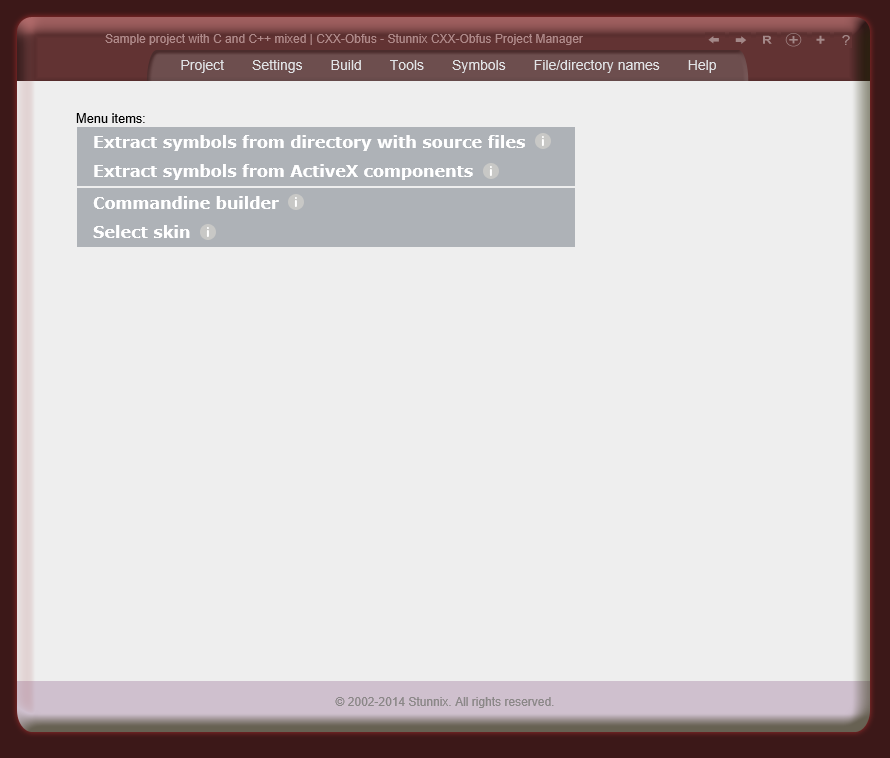
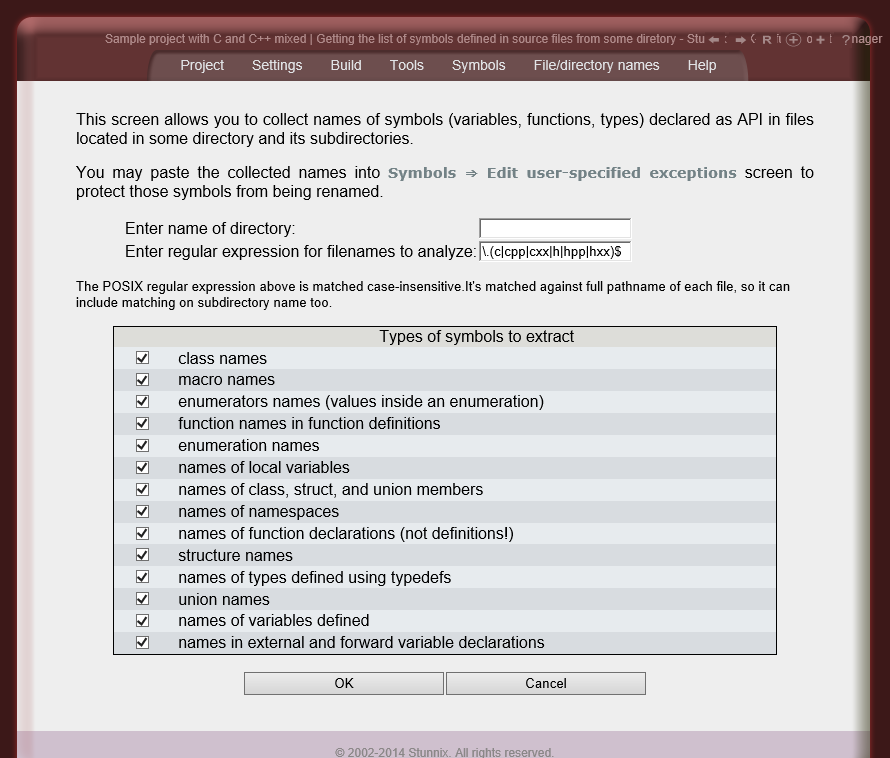
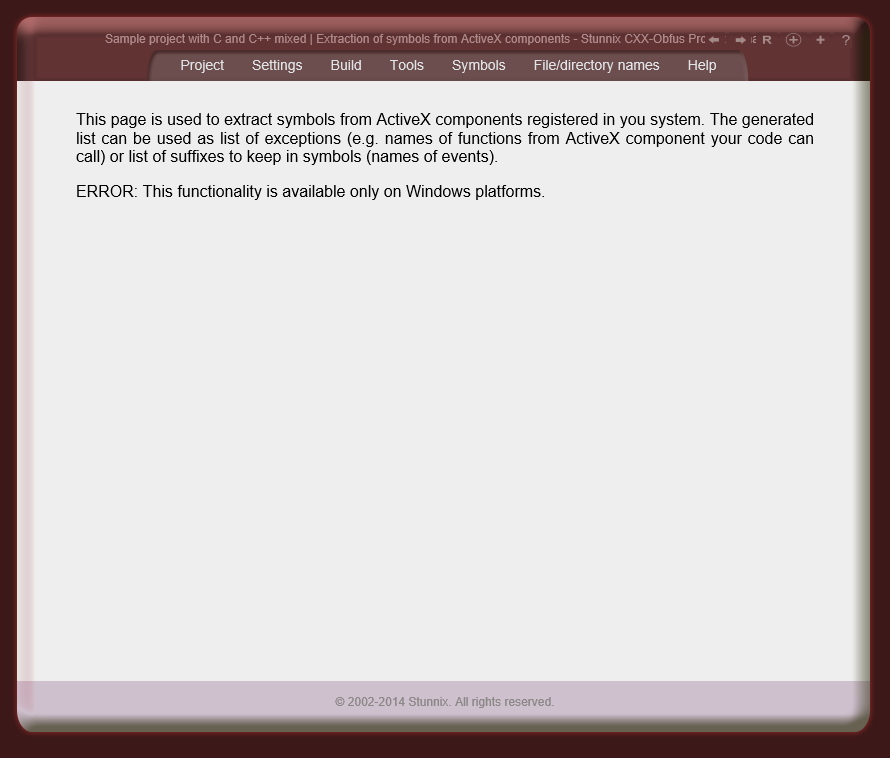
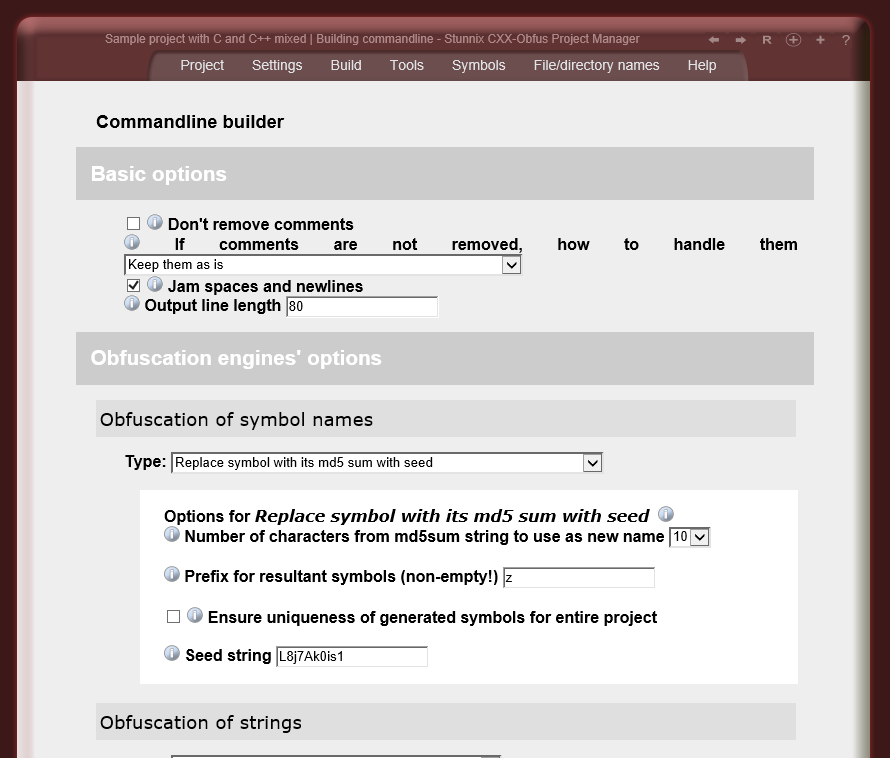
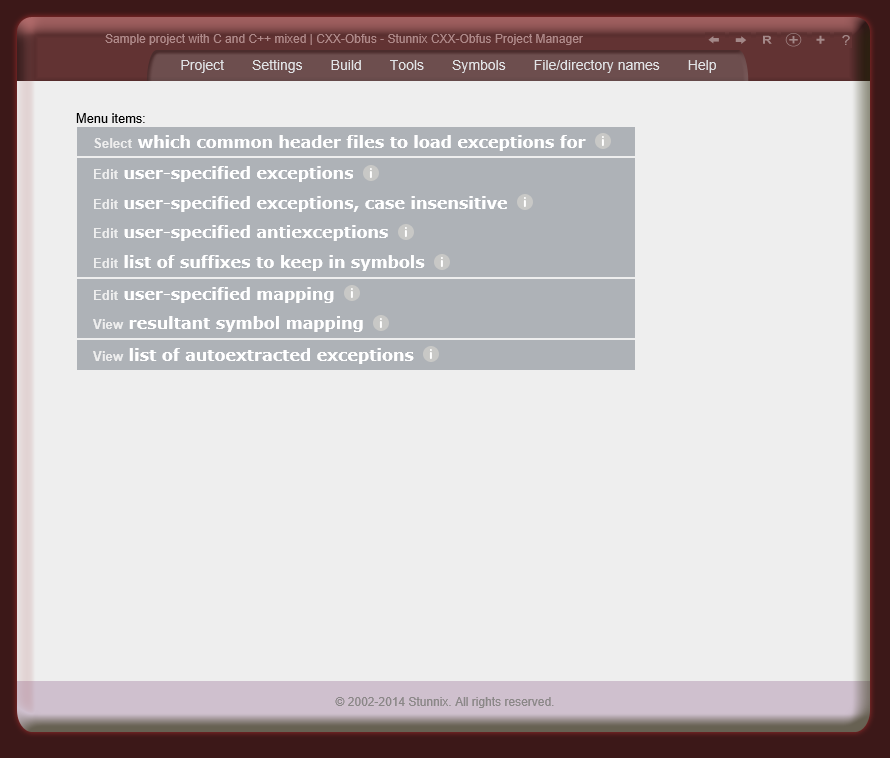
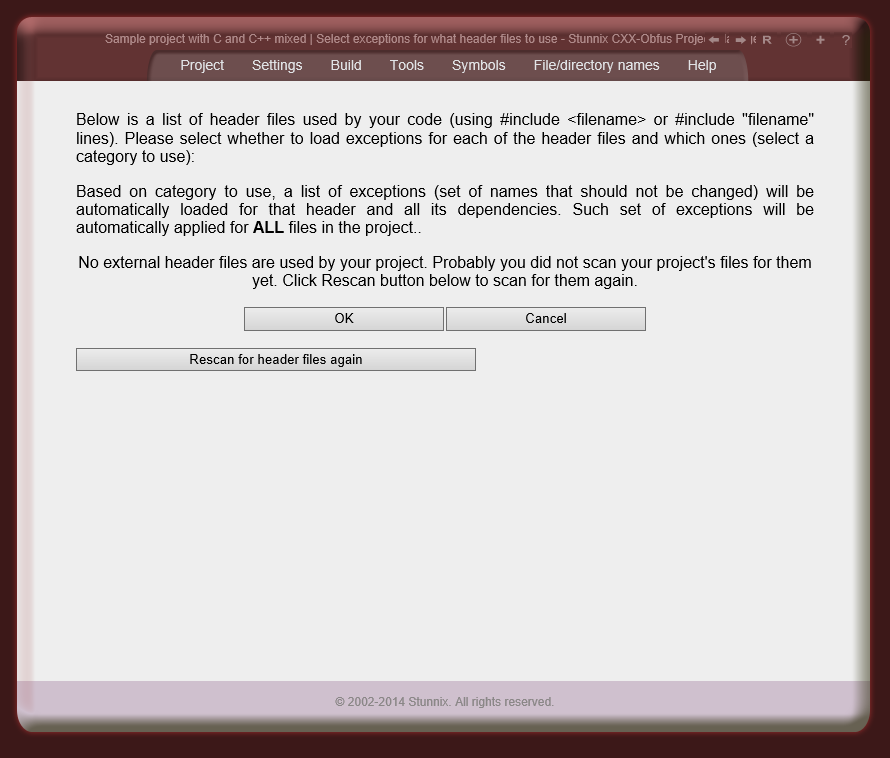
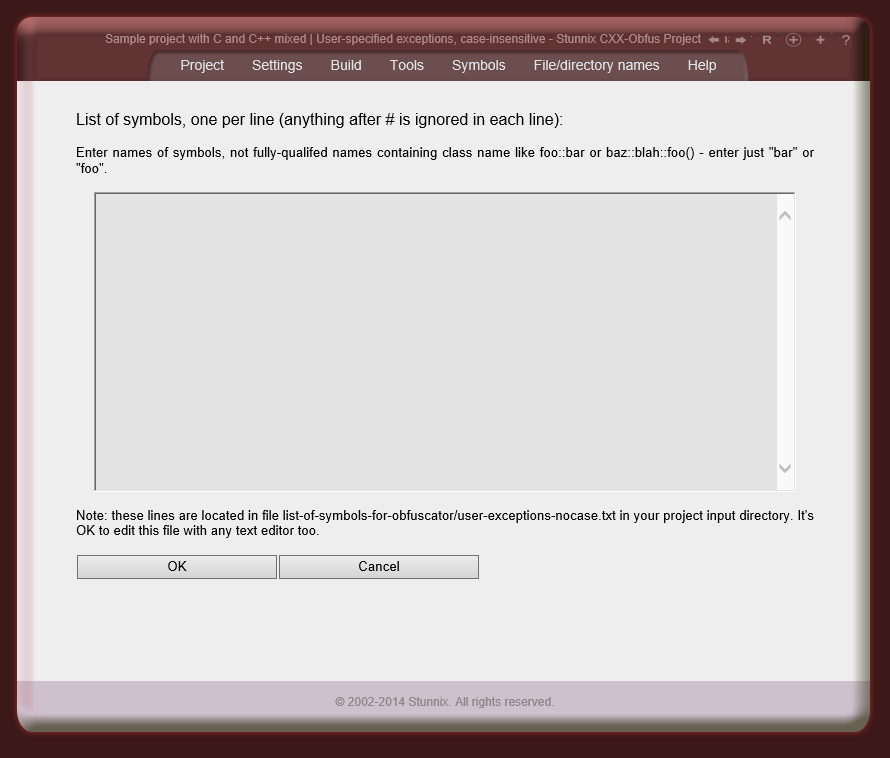
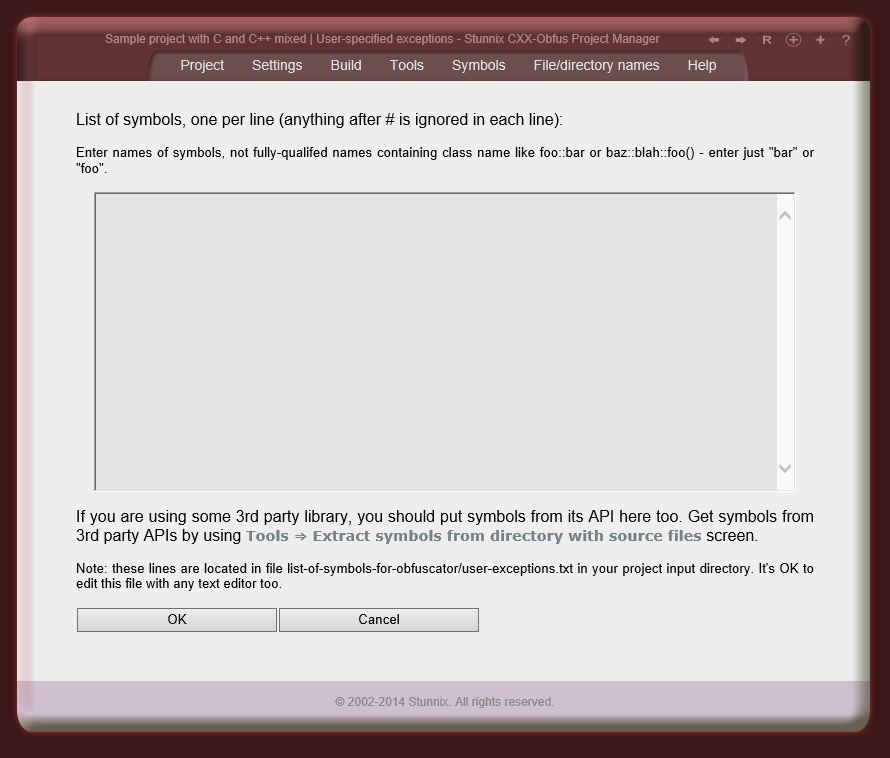
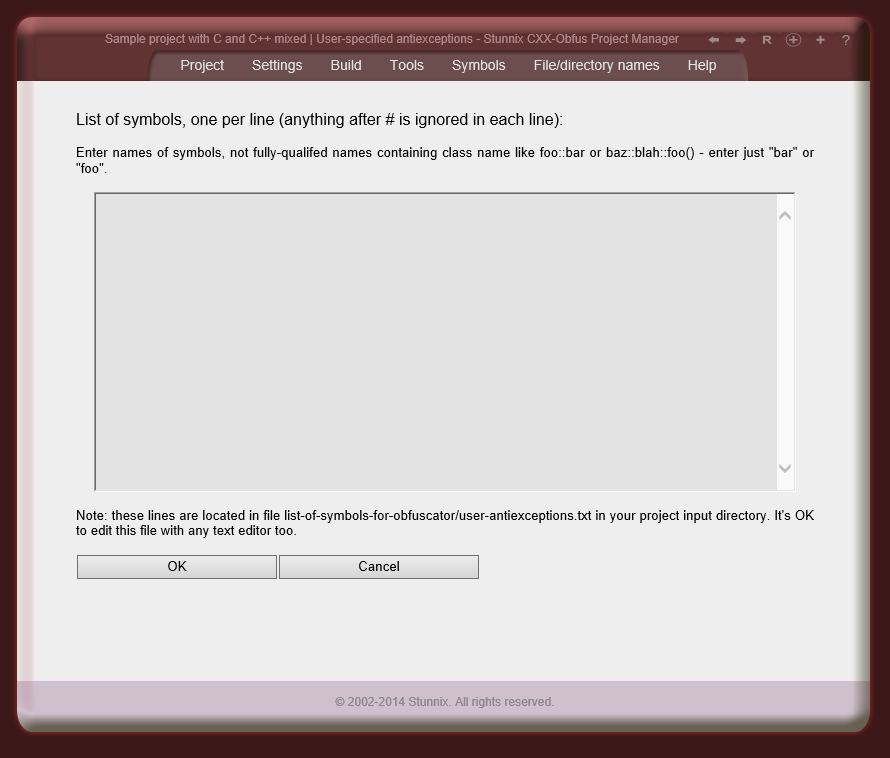
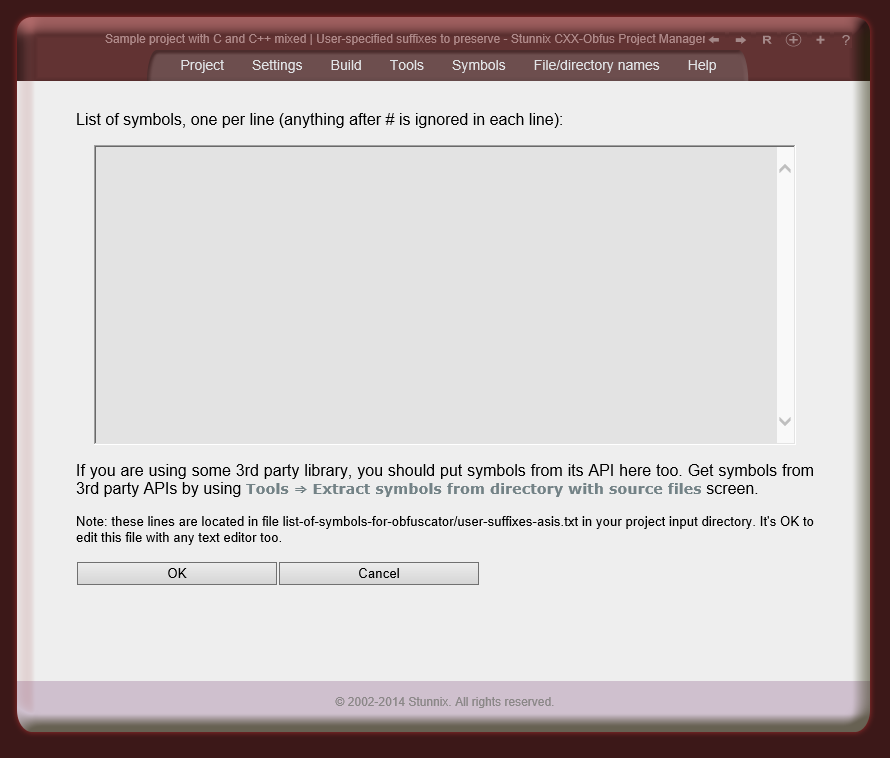
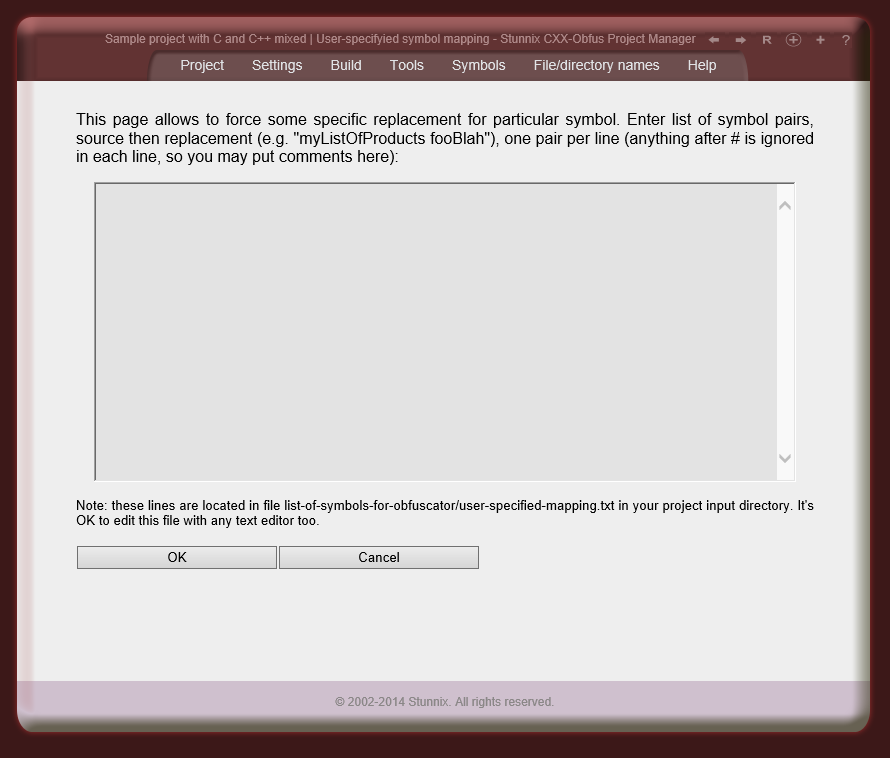
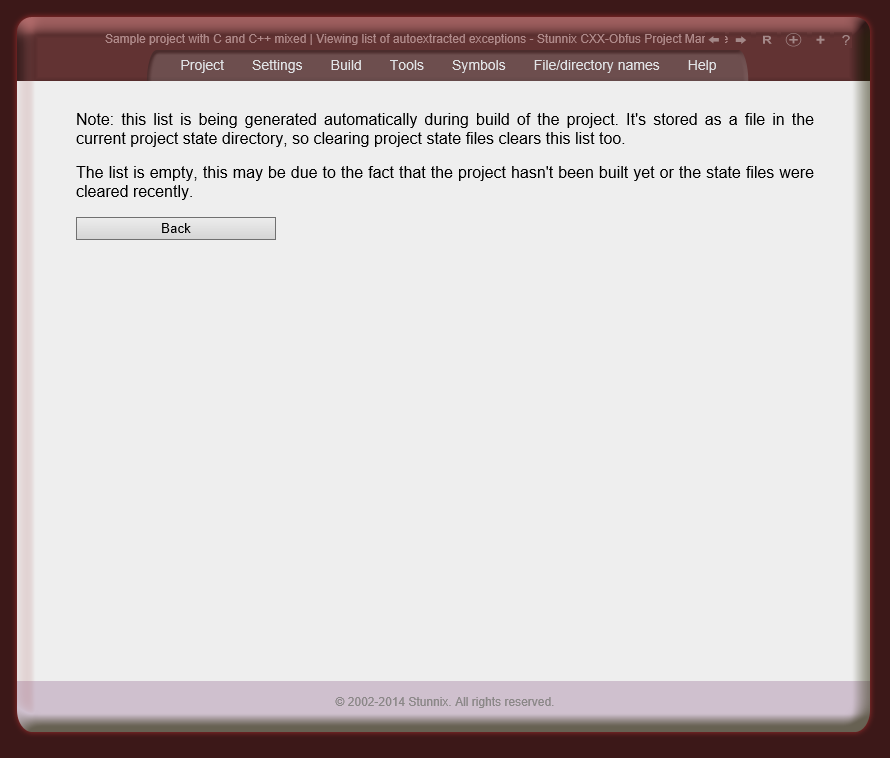
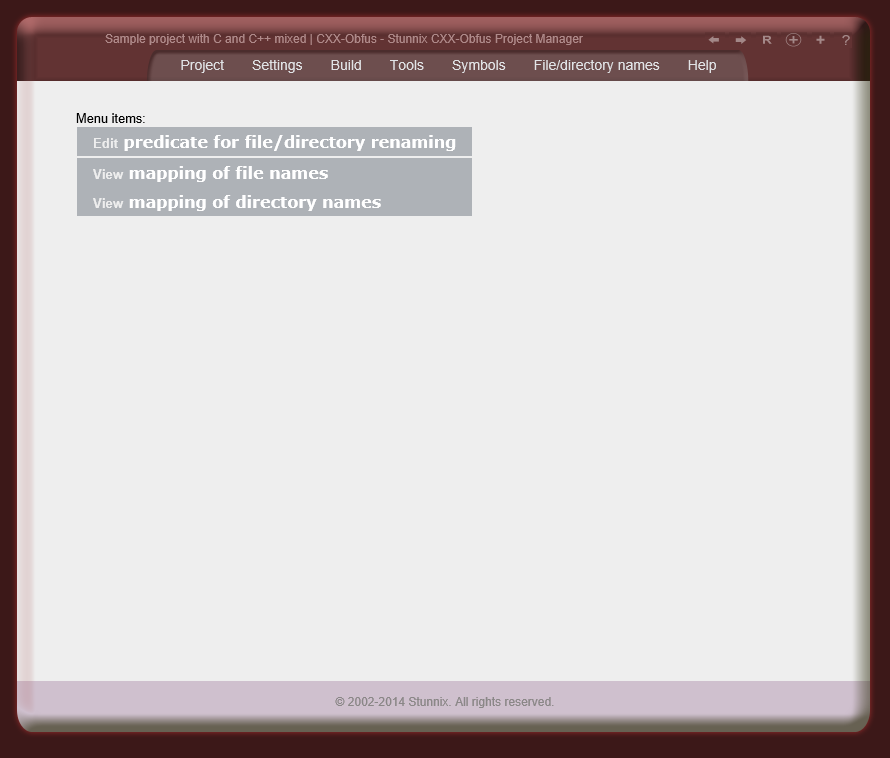
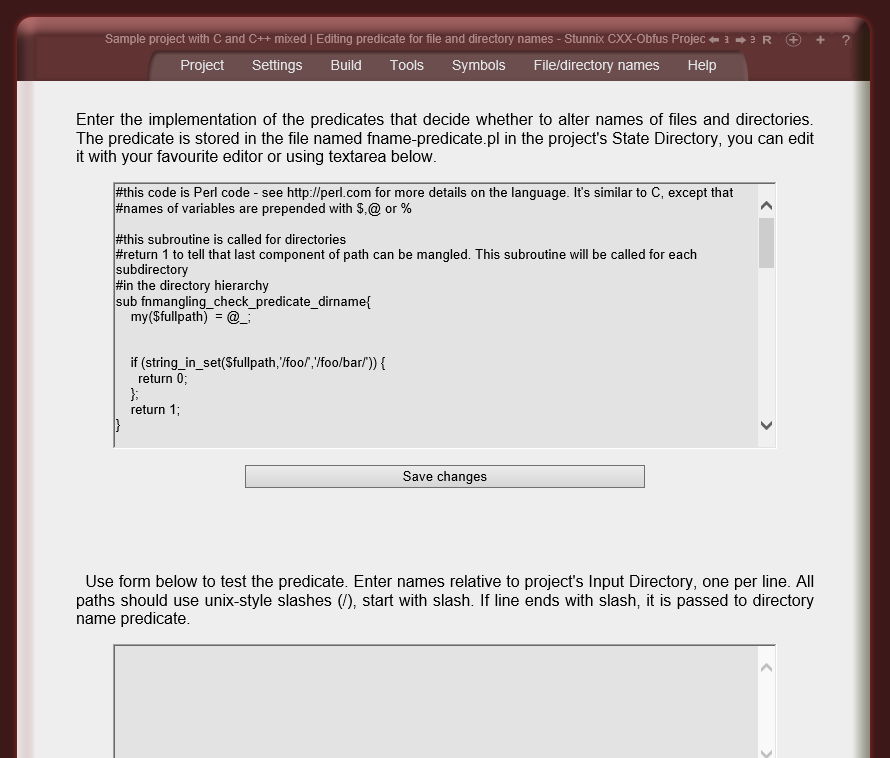
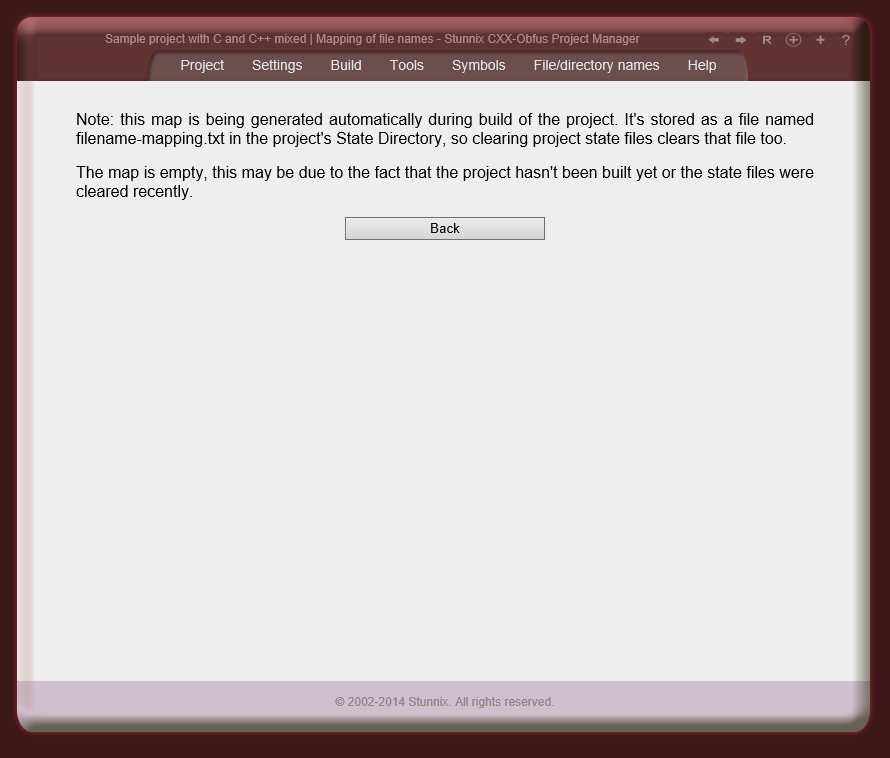
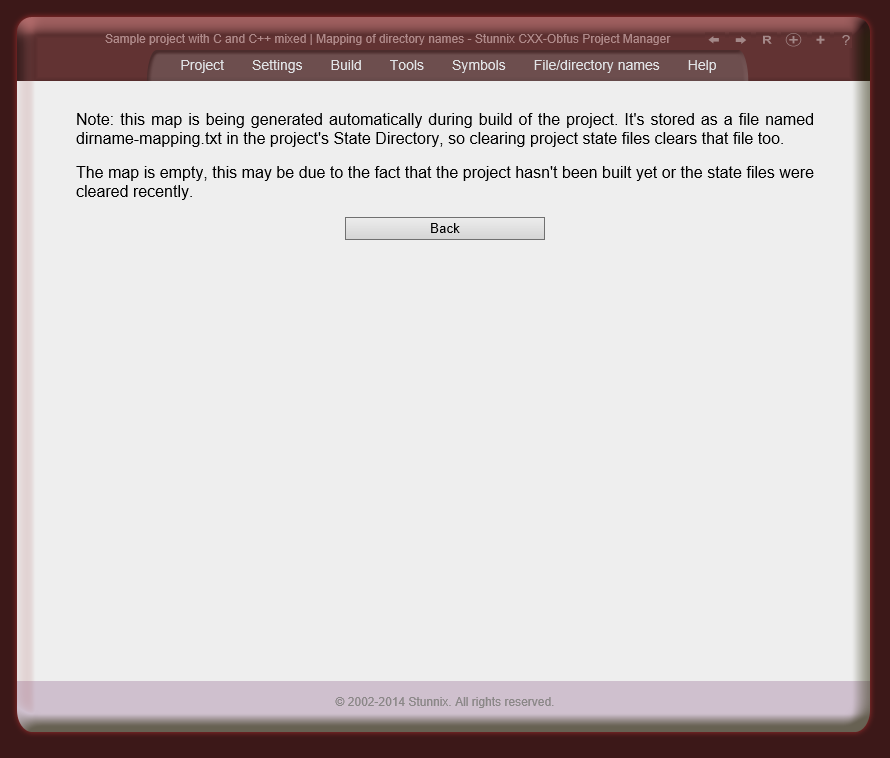
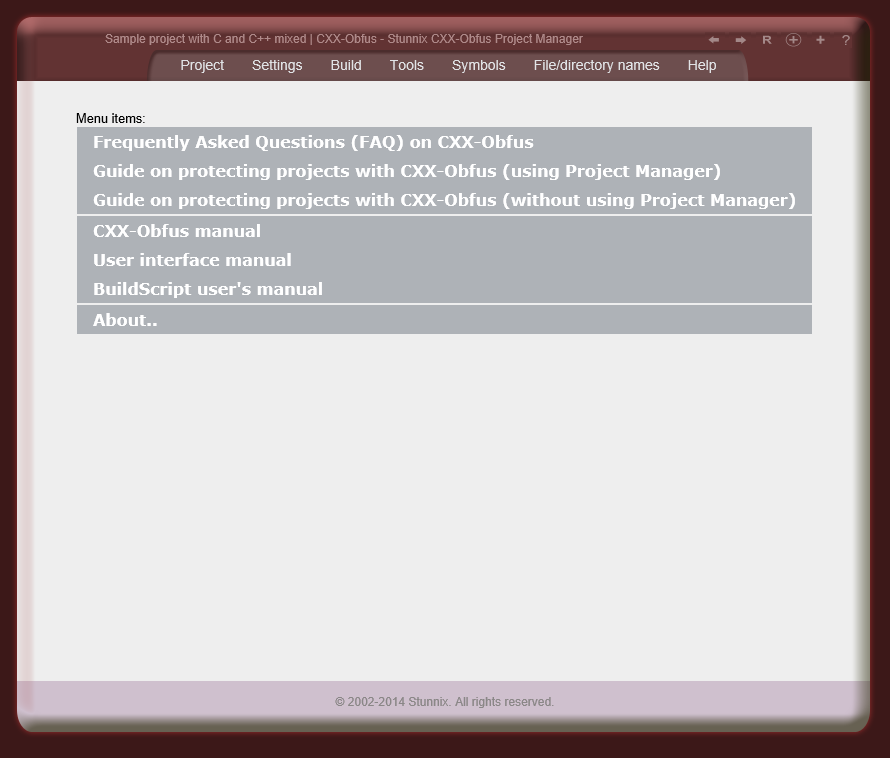
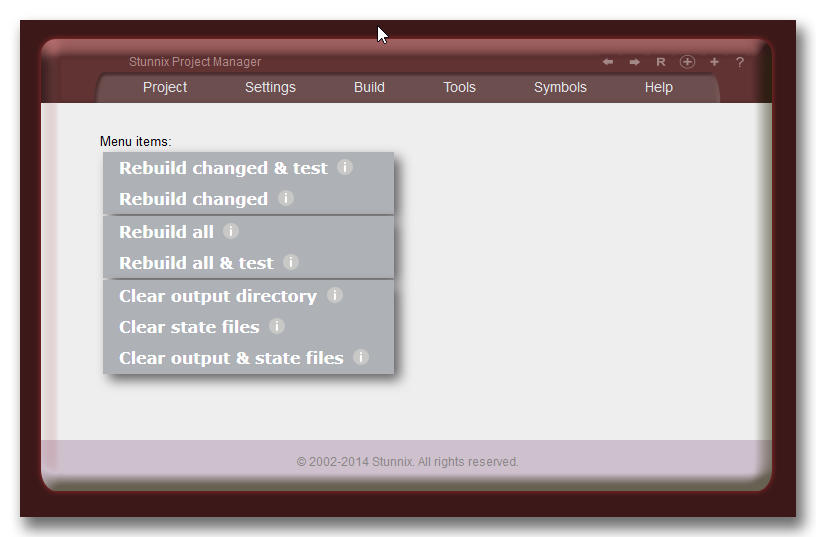
Screenshots of Project Manager tool
Below are screenshots of Stunnix C/C++ Obfuscator Project Manager GUI. There is a LIVE ONSITE demo of it too!
The obfuscation of C/C++ code means
Click on the small button "more info" below each item to expand details.
Replacing symbol names with non-meaningfull ones, e.g. replacing
list_of_customers with zcadaa4fc81
Replacing numeric constants with expressions, e.g. replacing 232 with
(0x14b6+2119-0x1c15)
Replacing characters in strings with their hex escapes, e.g. turning string
"cust" into "\x63\x75\x73\x74"
Unique!
Renaming files and directories with source code, e.g. renaming /lib/context.c into /7a84b51/b4e8c5.c
Removing or obfuscation of comments
Removing spaces and tabs in the lines of code
Joining all lines in your code
The features summary of C/C++ Obfuscator
Click on the small button "more info" below each item to expand details.
Unique!
C and C++ Obfuscator is cross-platform product, it
can be easily installed and used on Windows, Mac OS X,
Linux, Solaris or any other Unix OS.
Unique!
Supports correct obfuscation of
all preprocessor macros and conditionals of any complexity
Unique!
It can rename source files and directories with source files to make the code even more difficult to study.
Arguments of #include directive will be updated respecting the new (mangled) name of file and directory.
Unique!
Full support for products
consisting of several C and C++ files in the same C/C++ Obfuscation Project
Unique!
C and C++ Obfuscator includes Obfuscation Project
Manager - an advanced intuitive cross-platform (Windows, MacOS X, Linux and Unix)
graphical user interface for
protecting any size project created with C/C++ with mixed types of code ,
complete with with IDE-like functionality (supporting Build, Rebuild Changed,
Clean)
It can extract symbols for any API - just provide a directory with the files defining API
Unique!
C and C++ Obfuscator has special debugging mode
and unique tools to generate a list of symbols that can't be changed,
saving development time.
Unique!
C and C++ Obfuscator supports several advanced ways to generate obfuscated names including
using shortest possible name.
C and C++ Obfuscator supports all C/C++ dialects
of all existing compilers
Unique!
Many options to tightly control the obfuscation and encoding of C and C++ Obfuscator
Unique!
Ability to watermark C/C++ and to make the study of changes between versions of
the same file more difficult
Unique!
C and C++ Obfuscator allows creation of lists of symbols that shouldn't be modified;
Many exception tables for standard APIs and libraries are included
Used by a lot of companies